Built for High-Stakes Environments
See how iWatchU protects critical digital assets across different industries.
Protect Pricing & Checkout Integrity
For online stores, a changed digit or a swapped payment link can cost millions. iWatchU monitors your critical product pages and checkout flows.
- Detect unauthorized modifications to product prices or descriptions.
- Ensure "Buy Now" links haven't been hijacked by malicious scripts.
- Verify that injected ads aren't covering your actual products.

Defend Brand Reputation
Public-facing portals are prime targets for hacktivism. Defacing a homepage with political messages or offensive images destroys public trust instantly.
- Visual AI immediately flags "hacker logos" or drastically altered layouts.
- Monitors DOM structure to catch invisible SEO spam injections.
- Zero-delay Telegram alerts allow for rapid incident response and site takedown.

Prevent Fake News Injections
When millions rely on your platform for accurate information, bad actors may subtly alter headlines or articles to spread misinformation.
- Strict 5% deviation threshold triggers alerts on altered editorial content.
- Ignores expected dynamic changes like rotating ad banners.
- Maintains historical baselines to prove the original state of publication.

Secure User Workflows
Modern web apps are highly dynamic and rely heavily on third-party scripts. iWatchU ensures your critical user pathways remain uncompromised.
- Protects login portals and dashboard interfaces from script injection.
- Ensures third-party integrations (like chat widgets) haven't been hijacked.
- Monitors for unauthorized layout shifts indicating hidden overlay attacks (clickjacking).

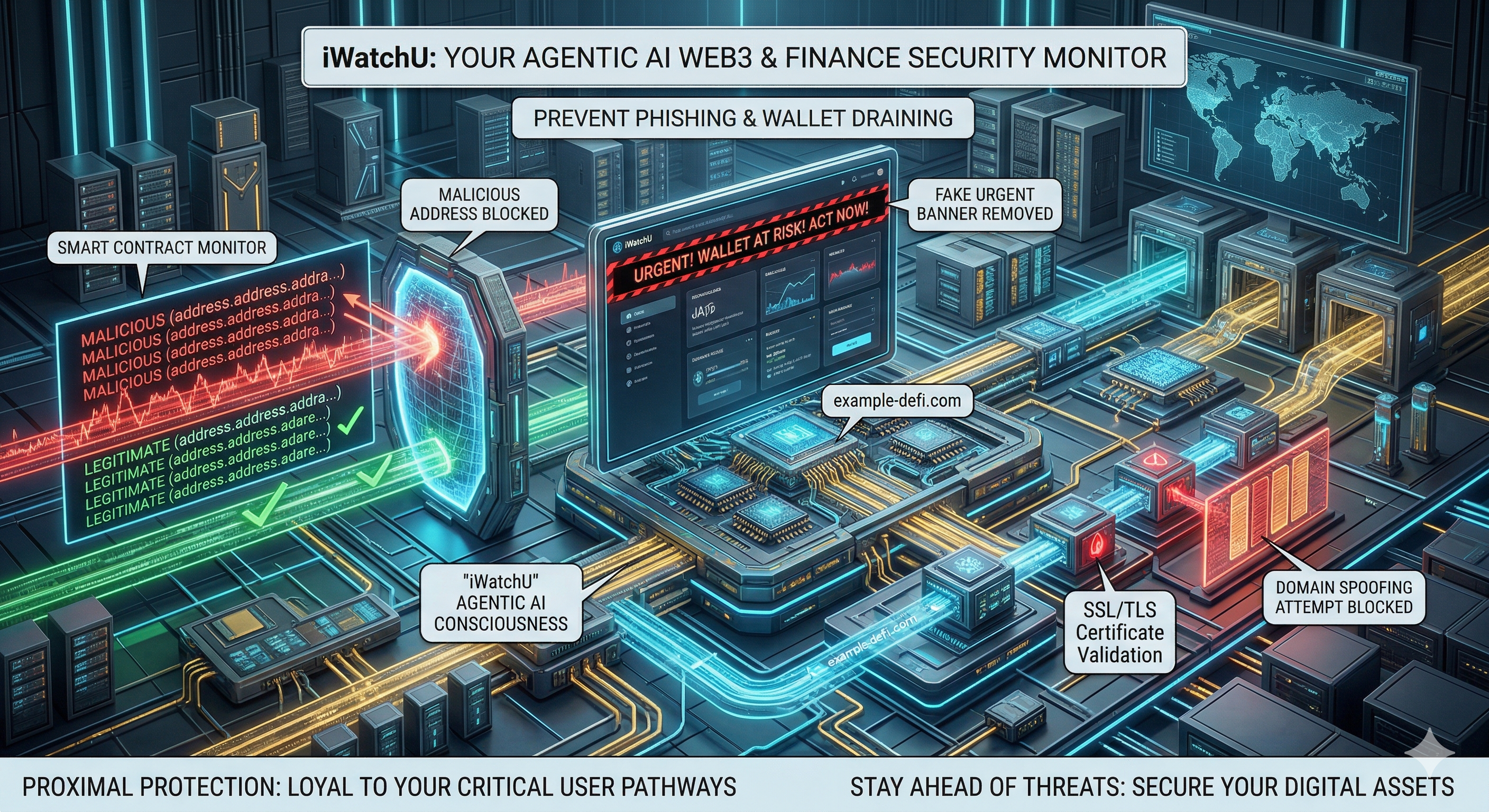
Prevent Phishing & Wallet Draining
In web3 and finance, a single swapped link or altered address can cause catastrophic financial loss for your users.
- Detects when legitimate smart contract addresses are swapped with malicious ones.
- Monitors for injected "urgent" banners meant to induce panic in users.
- Validates SSL/TLS certificates to prevent domain spoofing.