Zero-False-Positive
Security Engine
Go beyond simple text comparisons. iWatchU's advanced multi-layered AI evaluates structure, semantics, and supply-chain behavior to perfectly secure your digital perimeter.
The Threat DictionaryWhat our Sentinel detects automatically, 24/7.
1. Structural Guard
Mechanism: We monitor your page's structural skeleton. If a hacker injects hidden divs, malicious tracking pixels, or alters the DOM hierarchy, we know immediately.
Target: Unauthorized layout modifications and script placeholder injections.
2. Semantic AI Content Classifier
Mechanism: We don't just look for text changes—we analyze intent. Our AI evaluates text modifications to distinguish between routine updates and malicious SEO spam.
Target: Political manifestos, fake news injections, and scam announcements.

3. AI Vision Sentinel
Mechanism: Powered by Multimodal AI. We take automated, stabilized screenshots to look for visual defacement or broken UI elements that code alone might miss.
Target: Visual defacement, political graffiti, or obscured user interfaces.
4. Automated Site-Wide Discovery
Mechanism: We don't just protect the homepage. Our autonomous crawler discovers and maps all internal URLs, ensuring your entire digital perimeter is secured.
Target: Orphaned pages, hidden sub-directories, and newly added site content.
5. Supply Chain JS Inspection
Mechanism: Deep script inspection defends against MITM Magecart attacks. We actively monitor external JavaScript payloads to catch poisoning before data is stolen.
Target: Third-party script tampering and malicious external library injections.

6. DNS & SSL Monitoring
Mechanism: Proactive infrastructure monitoring. We continuously resolve A, MX, and CNAME records to detect DNS hijacking and inspect TLS certificates.
Target: DNS hijacking, IP mismatch, and preventable downtime from expired certificates.
The Portal ExperienceA single pane of glass for enterprise security.
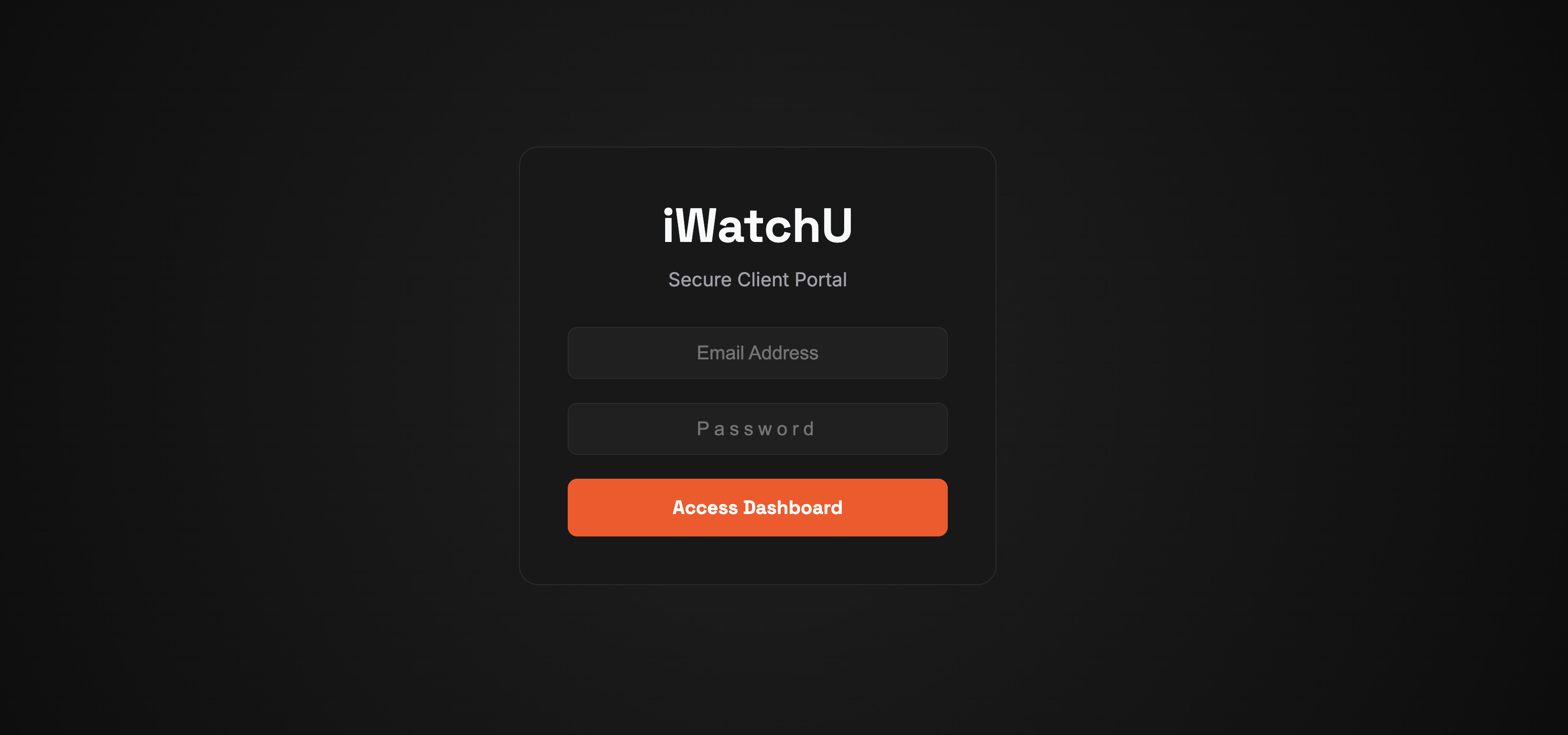
Enterprise Authentication
Secure JWT-based access with encrypted credentials ensures that only authorized administrators can control the surveillance grid. Instant feedback and lockdown measures protect your command center.
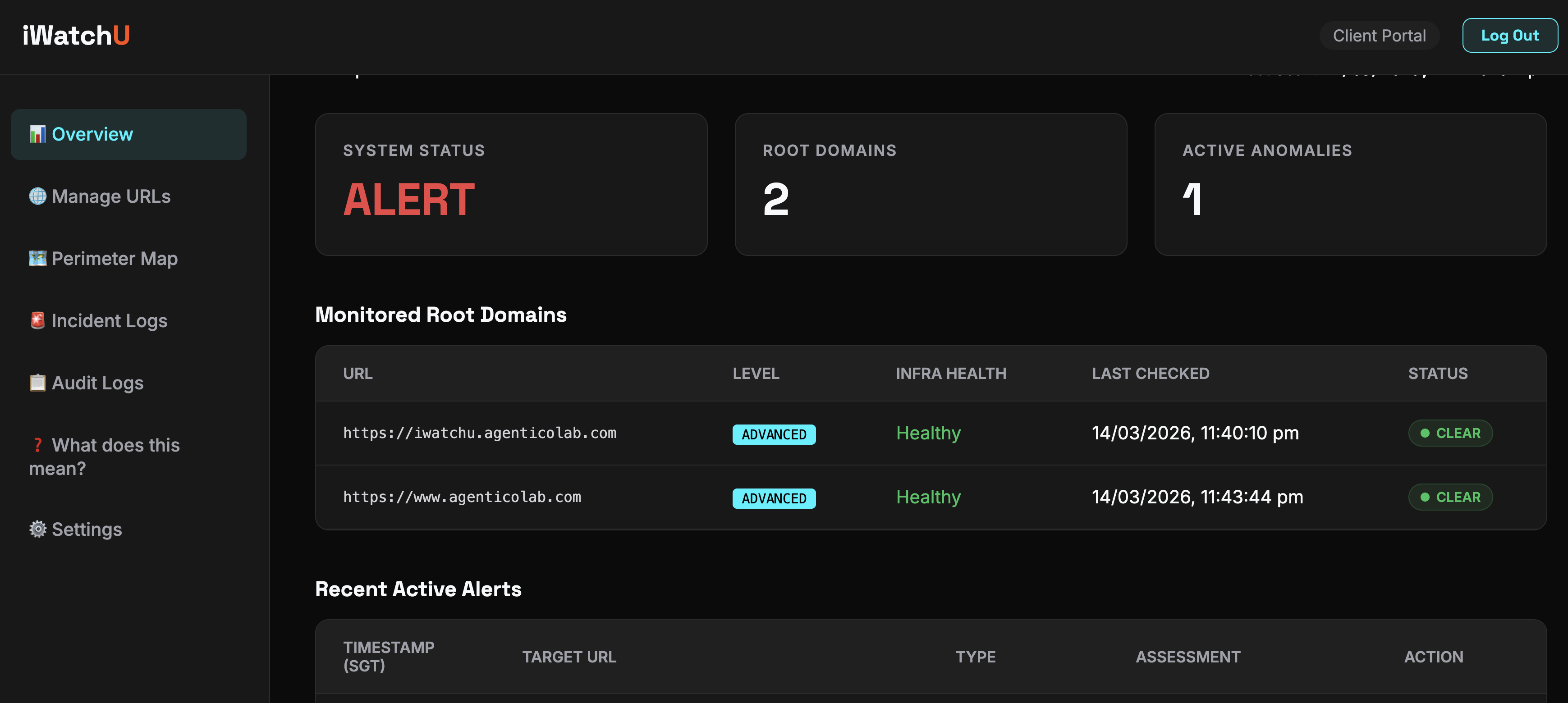
Real-Time Overview
Get a high-altitude snapshot of your entire digital real estate. See exactly how many endpoints are actively monitored, quota usages, and immediate systemic health alerts in an energetic, dark-themed dashboard.
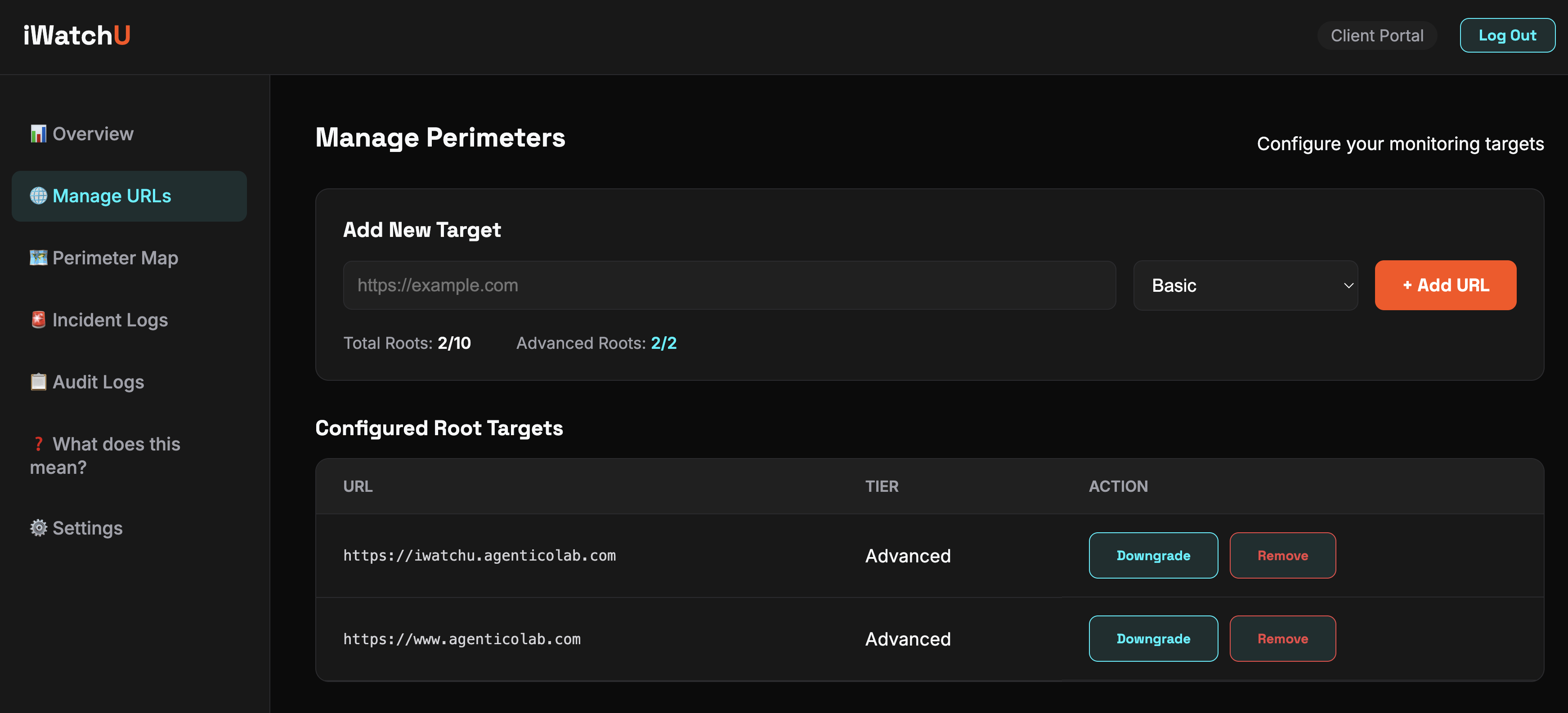
Flexible Perimeter Control
Add, remove, or upgrade monitoring tiers on the fly. Switch between Basic (Structural & Content) and Advanced (Vision AI & Supply Chain JS) tiers instantly without touching a single configuration file.
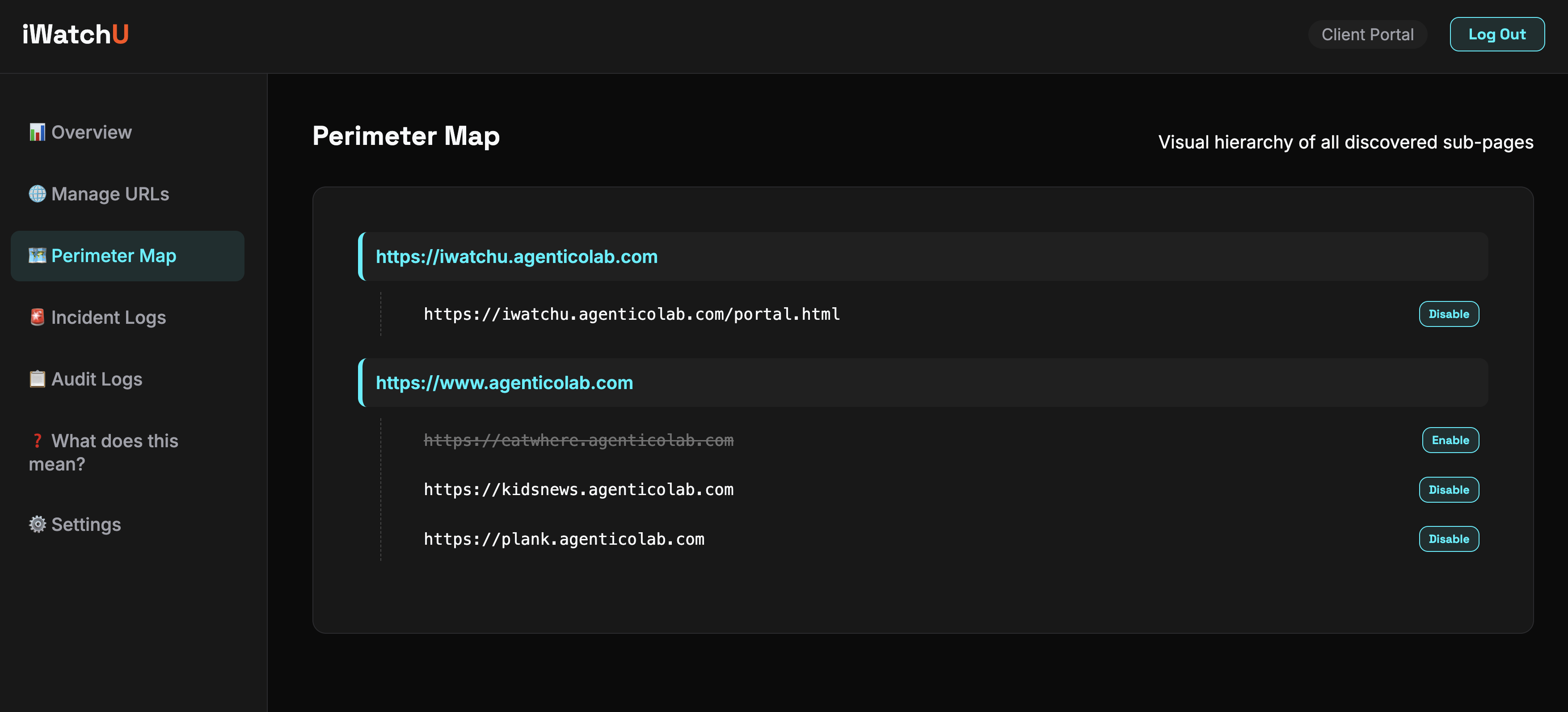
Auto-Discovery Map
Never leave an orphaned sub-page unprotected. Our aggressive Playwright crawler auto-discovers links across your domain, building a visual tree that lets you toggle protection on specific sub-directories with one click.
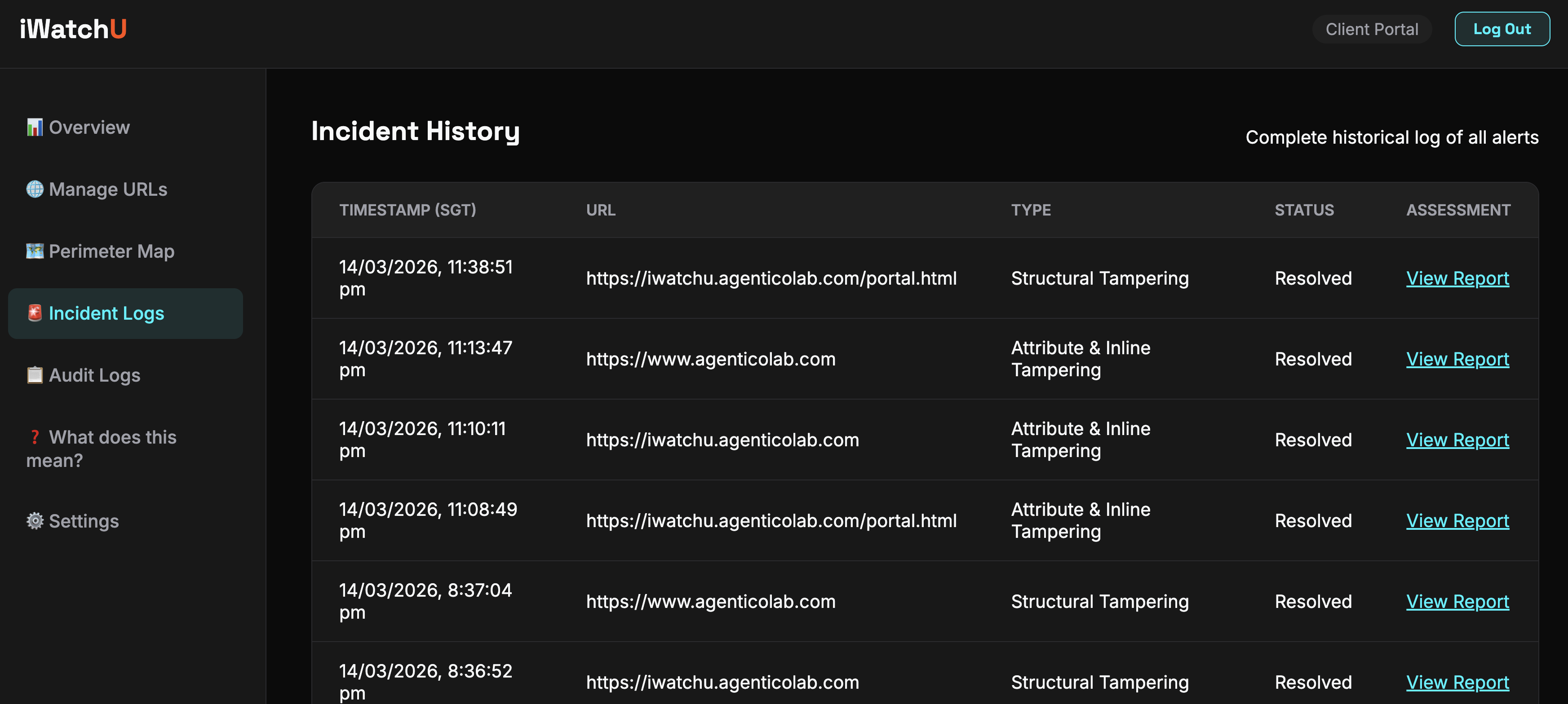
Forensic Incident Logs
When an anomaly is detected, you don't just get an alert—you get a full forensic breakdown. View exact line-by-line diffs, LLM assessments, and the precise layer of the attack to accelerate incident response times.